Zero‑Trust Architecture: The Future of Enterprise Security
Discover how Zero‑Trust Architecture is reshaping enterprise security. Learn the principles, benefits, implementation steps, and real‑world success stories.
Why the “Zero‑Trust” Buzz is More Than a Trend
Imagine walking into a high‑security vault that never assumes anyone inside is trustworthy. Every person, every device, every action is verified before access is granted. That’s the essence of Zero‑Trust Architecture (ZTA). In today’s cloud‑first, remote‑work‑ready world, the old “trust‑but‑verify” model simply can’t keep pace with sophisticated cyber threats.
If you’ve ever been hit by a ransomware attack, seen a data breach headline, or felt the pressure of tightening compliance standards, you know why enterprise security must evolve. The answer? A Zero‑Trust mindset—think of it as a security framework that treats every request as if it comes from an untrusted source, no matter where it originates.
What Exactly is Zero‑Trust Architecture?
Zero‑Trust isn’t a product; it’s a set of principles that guide how an organization builds and operates its security posture. The core ideas are simple:
| Principle | What It Means | Why It Matters |
|---|---|---|
| Never trust, always verify | Every user, device, and data request must be authenticated and authorized before access is granted. | Eliminates implicit trust based on network location. |
| Least privilege | Users and services only get the permissions they need to perform their tasks. | Reduces attack surface and limits damage if credentials are compromised. |
| Micro‑segmentation | Network traffic is isolated into small, secure zones. | Stops lateral movement of attackers. |
| Continuous validation | Security posture is monitored in real time. | Responds quickly to anomalous behavior. |
These principles were codified in NIST Special Publication 800‑207 and are now adopted by governments, Fortune 500s, and startups alike.
2. Why Zero‑Trust? The Threat Landscape
| Challenge | How Zero‑Trust Helps |
|---|---|
| Remote & hybrid work | Every device, wherever it sits, is verified. |
| Cloud & SaaS proliferation | Cloud workloads are treated the same as on‑prem resources. |
| Persistent threats (APT, ransomware) | Lateral movement is blocked by micro‑segmentation. |
| Regulatory pressure (GDPR, CCPA, HIPAA) | Built‑in least‑privilege controls aid compliance. |
In 2023 alone, 43% of data breaches involved a compromised user credential. Zero‑Trust’s layered verification process turns that single weak point into a multi‑layered defense.
3. The Pillars of Zero‑Trust Architecture
-
Identity & Access Management (IAM)
- MFA, Single Sign‑On (SSO), Role‑Based Access Control (RBAC).
- Example: Azure AD Conditional Access.
-
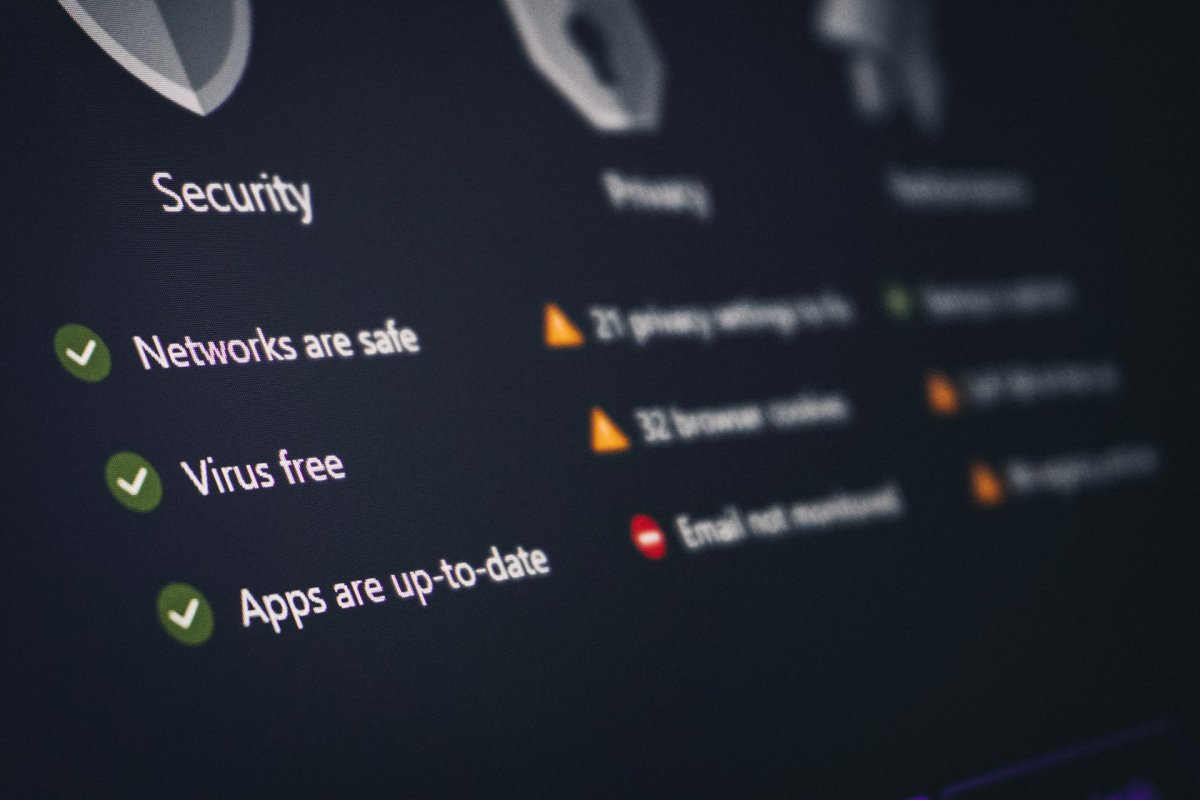
Device Posture
- Check for up‑to‑date OS, antivirus, encryption.
- Tools: Microsoft Defender ATP, CrowdStrike.
-
Network Segmentation & Micro‑segmentation
- Use virtual LANs, software‑defined networking (SD‑N).
- Example: VMware NSX‑T.
-
Data Protection
- Encryption at rest & in transit, data loss prevention (DLP).
- Example: Symantec DLP.
-
Continuous Monitoring & Analytics
- SIEM, SOAR, behavioral analytics.
- Example: Splunk, Palo Alto Cortex XSOAR.
4. Benefits You’ll Love
- Reduced Attack Surface – Lateral movement blocked; attackers can’t roam freely.
- Improved Compliance – Built‑in controls align with SOC 2, ISO 27001, NIST frameworks.
- Faster Incident Response – Continuous monitoring gives you real‑time alerts.
- Better User Experience – Seamless SSO & MFA means fewer login headaches.
- Future‑Proofing – Scales with cloud adoption, IoT, and emerging technologies.
5. How to Build a Zero‑Trust Roadmap (Step‑by‑Step)
| Phase | Action | Quick Wins |
|---|---|---|
| Assessment | Inventory assets, users, devices, data flows. | Use automated discovery tools (e.g., Microsoft 365 audit). |
| Prioritization | Identify critical assets, high‑risk users. | Protect your finance and HR systems first. |
| Policy Design | Define least‑privilege roles, segmentation zones. | Use RBAC templates for common roles. |
| Pilot | Deploy Zero‑Trust on a single business unit. | Test with a non‑critical department. |
| Expand | Roll out to other units, integrate with cloud services. | Adopt ZTA across SaaS applications next. |
| Optimize | Continuously refine policies based on analytics. | Set up dashboards for abnormal behavior. |
Tip: Don’t wait for a perfect plan—start small, learn, iterate.
6. Common Pitfalls & How to Avoid Them
| Pitfall | Why It Happens | Fix |
|---|---|---|
| Over‑complex IAM | Too many policies create confusion. | Use role templates; automate policy updates. |
| Ignoring Device Compliance | Devices slip through with missing patches. | Enforce conditional access that checks device health. |
| Siloed Teams | Security, IT, and business units work in isolation. | Adopt cross‑functional squads; use shared dashboards. |
| Skipping User Education | Employees still fall for phishing. | Run monthly phishing simulations and quick trainings. |
7. Real‑World Success Stories
| Company | Challenge | Zero‑Trust Solution | Result |
|---|---|---|---|
| Multiple data centers worldwide | Internal Zero‑Trust model, “BeyondCorp” | 100% of traffic goes through a secure gateway. | |
| Microsoft | Hybrid cloud migration | Azure AD Conditional Access + Microsoft Defender | Zero credential‑based breaches in 2024. |
| Capital One | Financial data at risk | Micro‑segmented microservices + MFA | Reduced internal lateral movement by 78%. |
These leaders demonstrate that Zero‑Trust isn’t a theoretical concept—it’s a proven strategy that delivers measurable security gains.
8. Zero‑Trust Tools & Technologies
| Category | Recommended Tools | Why It’s Useful |
|---|---|---|
| IAM & MFA | Okta, Duo, Azure AD | Seamless SSO & multi‑factor enforcement. |
| Device Posture | CrowdStrike, Qualys, Bitdefender | Real‑time health checks before granting access. |
| Micro‑segmentation | Palo Alto Networks, VMware NSX | Fine‑grained network isolation. |
| DLP | Digital Guardian, Symantec, Proofpoint | Detects and stops data exfiltration. |
| SIEM/SOAR | Splunk, LogRhythm, Palo Alto Cortex XSOAR | Unified threat detection and automated response. |
Pro tip: Many vendors now offer Zero‑Trust Network Access (ZTNA) as a SaaS, reducing the need for on‑prem appliances.
9. The Future of Zero‑Trust: AI, Automation, and “Zero Trust as a Service”
- AI‑Driven Risk Scoring – Predictive analytics identify anomalous user behavior before it escalates.
- Zero Trust as a Service (ZTaaS) – Cloud‑based ZTA platforms make enterprise‑grade security available to SMBs.
- Secure Access Service Edge (SASE) – Combines ZTNA, SD‑WAN, and cloud security in one package.
- Post‑Quantum Encryption – Preparing for quantum‑resistant cryptography as threats evolve.]
10. Frequently Asked Questions (FAQ)
| Question | Short Answer |
|---|---|
| What’s the difference between Zero‑Trust and traditional perimeter security? | Zero‑Trust removes the “perimeter” concept; every request is verified regardless of origin. |
| Can Zero‑Trust replace my firewall? | It complements, not replaces, firewalls. Zero‑Trust focuses on identity and data, while firewalls enforce network rules. |
| How long does it take to implement ZTA? | A pilot can take 3–6 months; full roll‑out varies, but a phased approach speeds adoption. |
| Do I need to change my existing apps? | Many cloud apps already support ZTA via SSO & MFA; legacy apps may require adapters or wrappers. |
| Will Zero‑Trust affect user productivity? | When implemented right, ZTA actually improves productivity by reducing login friction and support tickets. |
Conclusion: Take the Leap into Zero‑Trust Today
Zero‑Trust Architecture isn’t just a buzzword—it’s the security framework that will protect enterprises for the next decade. By shifting the paradigm from “trust the network” to “trust the identity,” organizations can stay ahead of attackers, meet regulatory demands, and empower a mobile workforce without compromising safety.
Ready to start?
- Begin with an asset inventory.
- Identify your high‑risk users.
- Choose an IAM solution that supports MFA and conditional access.
- Deploy a pilot in a low‑risk environment.
The future of enterprise security is already here. Embrace Zero‑Trust, and turn your organization into a resilient, adaptive, and secure entity—ready for whatever tomorrow throws at you.
You can check all my posts here.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Wow
0
Wow
0
 Sad
0
Sad
0
 Angry
0
Angry
0
















Comments (0)